Quick Fix: Get Computer Name from a Slave Drive…
April 13, 2011 6 Comments
Arrgh!
So a client called with a PC that crashed and wouldn’t boot up.
Luckily i was actually in the area so i called in to the customer, unluckily i was travelling light and didnt have my USB/SATA kit with me.
PC was a reasonably new Dell Optiplex 380, Running Windows 7 Pro. Covered under warranty and after a few minutes on the Dell Online Chat, i had arranged an engineer to be onsite next day with a new drive.
I decided to take the drive with me to see if i could salvage anything, and possibly image the drive for future recovery use.
So i brought the disk back to the office and set it up on a bench, ran a chkdsk and after that it seemed to function ok. (i could have done this onsite with an OS disc, but if it failed once i would rather have a new drive thank you)
So Dell have now replaced the drive and installed the OS, buuut wait, they dont join it to the domain or install any apps.
I need to know the name of this pc to rejoin it to the domain, i could make up a new name, but we have a convention… seems as though the system name sticker is missing as well.
So here’s what you can do.
Load up Regedt32 on the lab system, with the drive attached as a slave.
Navigate to HKLM and click file, load hive.
Now browse to the \windows\system32\config folder on the slave drive and find the SYSTEM file.
Enter a name – i used OLD
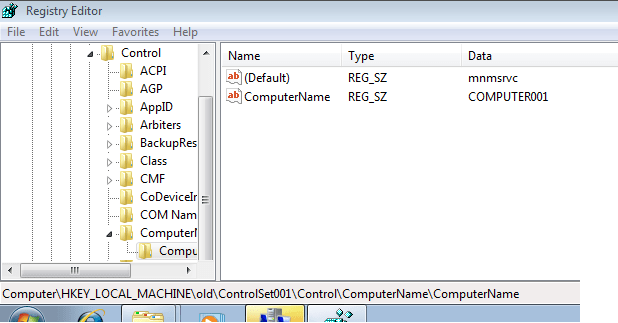
Now browse to HKLM>Old>CurrentControlSet1>Control>Computername>Computername
You should see a key named ‘ComputerName’ with the system name as the value.
Easy!
AWESOME! This worked perfectly! Thanks soooo Much!
Your is the first set of instructions that have actually worked. Well done, mate, and thanks very much!
Incredibly useful. Can also catch the users peeling the name tags off!
Worked for me. All the other solutions involved looking for non-existent files somewhere in the windows directory. Thank you!
Just wanted to thank you for this. Was a bit worried about the age of it.
Worked on a Windows 10 drive like a champ!
I had done the usual stuff with powershell on a corrupt drive with no luck.
This method worked! Thanks for this post!